Furthermore, where do you put an extended ACL?
Extended ACL "Should be placed closest to the source network." because it filter base on much more specific criteria such as source, destination ip address, protocol and port number.
Likewise, what is extended access list? Extended Access Control Lists (ACLs) allow you to permit or deny traffic from specific IP addresses to a specific destination IP address and port. It also allows you to specify different types of traffic such as ICMP, TCP, UDP, etc.
One may also ask, where should you place a standard ACL?
Standard Access Control List (ACL) filters the traffic based on source IP address. Therefore a Standard Access Control List (ACL) must be placed on the router which is near to the destination network/host where it is denied.
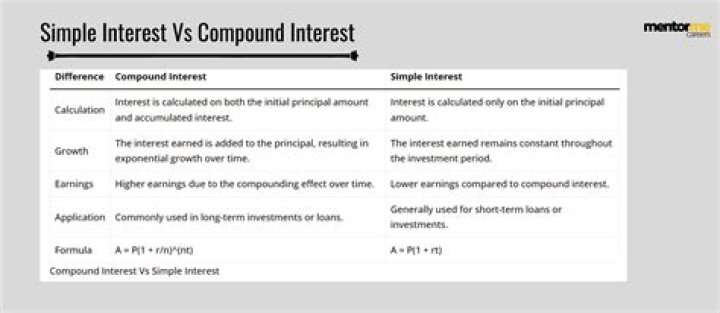
What is the difference between standard and extended ACL?
A “Standard” ACL allows you to prioritize traffic by the Source IP address. An “Extended” ACL provides greater control over what traffic is prioritized. Extended ACLs can use any or all of the following parameters: Protocol ID (RFC1700)
What are the different types of access control lists?
There are two main different types of Access-list namely:- Standard Access-list – These are the Access-list which are made using the source IP address only. These ACLs permit or deny the entire protocol suite.
- Extended Access-list – These are the ACL which uses both source and destination IP address.
How does Cisco Show ACL?
To display all IPv4 access control lists (ACLs) or a specific IPv4 ACL, use the show ip access-lists command.How does extended ACL apply filtering?
Filters Using Extended Access Lists. Extended ACLs compare the source and destination addresses of the IP packets to the addresses that are configured in the ACL in order to control traffic. Extended ACLs also provide a means to filter traffic based on specific protocols.What is standard access list?
Access-list (ACL) is a set of rules defined for controlling the network traffic and reducing network attacks. ACLs are used to filter traffic based on the set of rules defined for the incoming or out going of the network. Standard Access-list – These are the Access-list which are made using the source IP address only.Where is access control list?
Access control lists (ACLs) are important in two locations inside the network: on network infrastructure components such as routers, and on file servers. On a router or switch—essentially any device capable of routing traffic from one segment to another—you can implement an ACL to help control the flow of traffic.Which type of ACL can filter based on the source IP address?
ACLs are packet filters that can be implemented on routers and similar devices to control the source and destination IP addresses allowed to pass through the gateway. Standard access lists can filter on source address. Extended access lists can filter ICMP, IGMP, or IP protocols at the Network layer.What are the ranges for extended ACLs?
It is even possible with an extended ACL to define what protocol that is being permitted or denied. As with standard ACLs, there is a specific number range that is used to specify an extended access list; this range is from 100-199 and 2000-2699.What guideline is generally followed about the placement of extended access control lists?
What guideline is generally followed about the placement of extended access control lists? They should be placed as close as possible to the source of the traffic to be denied. They should be placed as close as possible to the destination of the traffic to be denied.How do I setup my standard ACL?
To create a standard access list, enter the ip access-list standard global configuration command. Identify the new or existing access list with a name up to 30 characters long beginning with a letter, or with a number. If you use a number to identify a standard access list, it must be between 1 and 99.Which identification number is valid for an extended ACL?
The range of standard ACL is 1-99, 1300-1999 so 50 is a valid number for standard ACL.Cisco Certified Network Associate (200-125)
| Access list type | Range |
|---|---|
| Standard | 1-99, 1300-1999 |
| Extended | 100-199, 2000-2699 |
Which type of access list should be placed closest to the source?
Extended access lists should be placed as close to the source as possible. This prevents unwanted traffic from passing through the network.What is ACL configuration?
One of the simplest ways of controlling the traffic in and out of a Cisco device is by using access lists (ACL). These lists are generally composed of a permit or deny action that is configured to affect those packets that are allowed to pass or be dropped.What is ACL command?
Access List Commands. An access control list (ACL) consists of one or more access control entries (ACEs) that collectively define the network traffic profile. This profile can then be referenced by Cisco IOS XR Software software features such as traffic filtering, priority or custom queueing, and dynamic access controlWhat is ACL and how it works?
The Anterior Cruciate Ligament (ACL) is the primary restraint to forward motion of the shin bone (tibia). The ACL prevents the tibia from sliding too far forward. The ACL also contributes stability to other movements at the joint including the angulation and rotation at the knee joint.Why standard ACLs are placed close to the destination?
Standard ACLs should be applied close to the destination of the packets so that they do not unintentionally discard packets that should not be discarded.How do you create an access list?
Creating a Named Access List to Filter on Source Address- enable.
- configure terminal.
- ip access-list standard name.
- remark remark.
- deny {source [source-wildcard] | any} [log]
- remark remark.
- permit {source [source-wildcard] | any} [log]